In the era of increasing digitalization and networking of all areas, software solutions are also increasing rapidly. Along with this, the number of so-called “lines of code (LoC)” constantly grows as well. Electric cars, charging stations, and industrial production facilities are affected by that, for example.
Today, an average compact car has around 100 million LoC compared to ten years ago, when it was just one-tenth of that figure with 10 million LoC. In addition, the number of updates and software upgrades is constantly rising.
Continuously developing complexity increases the susceptibility to errors and creates a significantly higher risk of vulnerabilities. Furthermore, this complexity drastically reduces the transparency of the software. Precisely here, the CVE database provides clear information!
What is CVE, and why is it important that I know what CVE means?
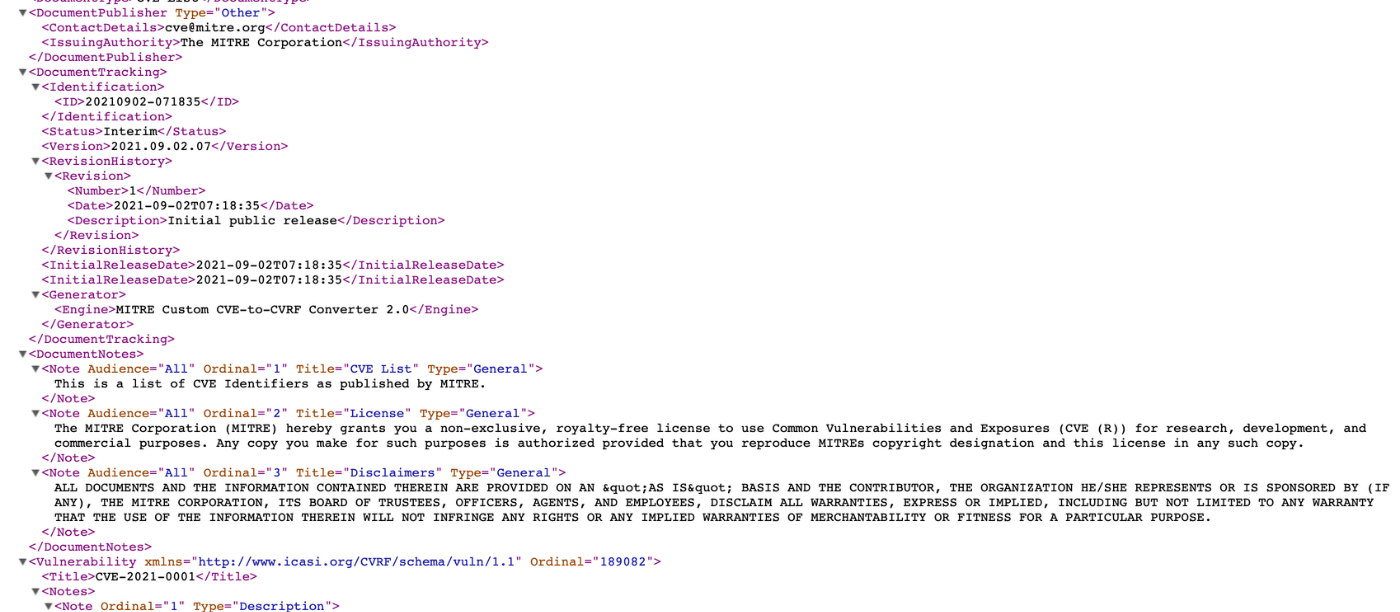
The “Common Vulnerabilities and Exposures” (CVE) database is one of the largest centralized databases for listing software vulnerabilities. The CVE database identifies, defines, and catalogs cybersecurity weak points that have become publicly known.
The identified vulnerabilities are published with a date, information about the product affected, and a description of the impact.
Unlike in software development, vulnerabilities are titled with the scheme CVE-YYYY-NNNN instead of using a descriptive word. Here, “YYYY” stands for the year in which the vulnerability was detected. “NNNN” uniquely identifies the weak points as a sequential number.
What does CVE Database serve?
In 2010, 4653 vulnerabilities were recorded in the CVE database. In 2020, there were 18325 entries – almost four times more. The trend of increasing software components in products with simultaneous neglect of protection can also be observed here clearly.
The CVE database is managed and maintained by the U.S. Department of Homeland Security (DHS), the Cybersecurity and Infrastructure Security Agency (CISA), and The MITRE Corporation, among other things.
The database currently contains 157,916 entries (as of 07/28/2021) on vulnerabilities in various software products – from cars to industrial equipment to smart home devices, such as a smart heating control for your home.
First and foremost, the CVE database serves to protect consumers. In addition, transparency is created regarding possible risks from software vulnerabilities and security gaps, and rapid remediation by the distributing company is promoted.
What does this mean for my company and me?
For a company that sells a software product or a product with software components, an entry in the CVE database, as opposed to a mention in relevant media, is anything but desirable. A CVE entry shows that you do not have your software under control or that your software does not meet the highest current security standards. Today, a vulnerability analysis to determine possible weaknesses is essential for the successful and competitive marketing of a product, besides the sheer testing of the functionality of your software.
This can be done by using established tools to access the CVE database, to ensure, for example, that you don’t trade vulnerability through a supplier’s product.
Unfortunately, there are hardly any freely available tools today. Open Vulnerability Assessment Scanner (OpenVAS), an open-source tool, is often used as the first contact point. Further tools can be found in the OWASP listing at https://owasp.org/www-community/Vulnerability_Scanning_Tools.
Should I be Afraid of CVE Entries Now?
There is a clear answer to this – fear not but do worry!
Of course, a CVE entry is not a desirable goal for your company, but it clearly shows you how to identify the needs for action and initiate improvements. Furthermore, the absence of CVE entries for your products does not directly mean that you have no security vulnerabilities at all.
Your cybersecurity must follow a holistic plan. A plan can be developed and implemented, for example, by using a classic ISMS based on the ISO 270xx family.
We, Tagueri AG, offer you the whole range of security instruments, from code reviews of your software products, quick checks of your organization, employee trainings to penetration testing of your servers and IT landscape, as well as support you in the implementation of your tailor-cut holistic cybersecurity plan.
Together we can master the future!