Protect your Data with Multiple Factors
What is Multi-Factor Authentication?
It is nothing new that login data is stolen through phishing and/or passwords are negligently revealed to third parties. However, with an access restriction that is only protected by one factor – the most common protection is the username-password principle – access can be granted directly after a successfully executed phishing attack.
But how can you use multi-factor authentication (MFA) to make your company infrastructure more secure and protect your corporate data?
Three Types of Multi-Factor Authentication
Of course, it makes no sense to use two passwords for one access, which you must enter one after the other. Security would increase only minimally since both passwords can be phished as well. It is better to restrict access in several independent ways. For this reason, we distinguish the different factors of multi-factor authentication into the three types:
-
Knowing (via secret information)
-
Having (via physical equipment)
-
Being (via body authentication)
What Does “Knowing” Mean?
Secret information is the most commonly used factor for identity verification. Logging into the mailbox, unlocking Bitlocker hard disk encryption, or logging into the personnel management system for time recording or collecting payroll, passwords, security questions, or entering PIN codes are the most common method of authentication. Only the user himself must know this secret information.
Do you already know how to create secure passwords that everyone can easily remember? You can read the relevant article here.
What Does “Having“ Mean?
By authentication with physical equipment, a user can confirm his identity, for example, by a smart card or a token, and by his smartphone with a unique phone number. In addition, you can use various smartphone applications (Google Authenticator, Microsoft Authenticator) and hardware devices (YubiKey, SecurID token).
Was Does “Being“ Mean?
Authentication though physical body means applying the specific physical characteristics of a user. Biometric data such as the fingerprint, the iris, or the voice are characteristics that are unique to each person and can identify a user in a largely forgery-proof manner. Many laptops and smartphones now have built-in fingerprint scanners or use the camera for facial recognition. However, no two people are known to have the same fingerprint to date.
What are the Advantages and Disadvantages of Each Factor?
Have you ever seen a password written down on a post-it and stuck to the edge of the screen? Despite all warnings, this method of facilitating access still occurs. Even if entering a password, PIN, security pattern, or answering a security question is easy, so is the authentication method – especially if it is the only method.
Physical equipment is a different story. No one can easily forge or phish possessions. You would have to steal it physically. The disadvantage here is that things can also be lost or forgotten.
Since physical characteristics are unique, strangers cannot imitate them. Likewise, these authentication methods consist of complex data sets (fingerprint, iris, voice), but adapted hardware is needed to record them. In addition, these store personal physical characteristics. Loss of these physical characteristics, such as an amputated thumb, can invalidate access authorizations.
Only the combination of two or more factors ultimately gives you increased security and protects your company data optimally.
The following overview presents various options for implementing multi-factor authentication and compares them based on selected criteria.
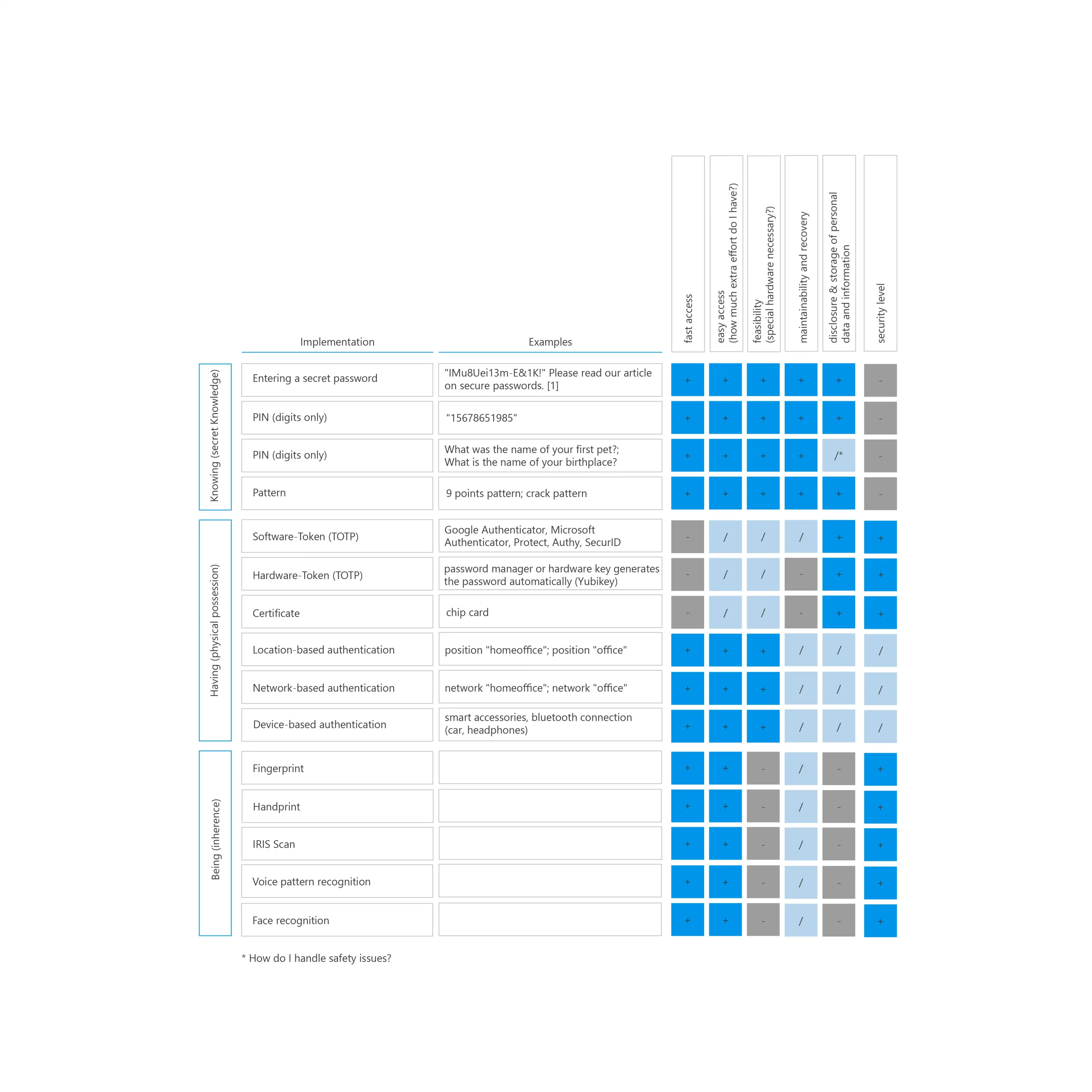
Figure 1 – Overview of Authentication Factors
How Does Multi-Factor Authentication Work in Practice?
The first and most common login factor for a user is the entry of a secret password or PIN, which only the user is allowed to know. If the user could authenticate himself correctly by entering the password, he must authenticate himself again with the second factor. In the second stage, a second device generates an additional PIN. Here, you can use a hardware token or an authenticator app on the company phone to display the PIN code. You can also use automatic login hardware that generates an unknown new one-time password (OTP) as a second factor for login.
The important thing here is that two factors of different classes are required when the user logs in, as in the example given, secret information (knowing) and physical equipment (having).
If the system has authenticated both factors, the user gets access to company emails and data. However, for an unauthorized third party who has possession of the password without access to the second necessary factor, there is a slight possibility of bypassing the authentication process and thus gaining access to sensitive company data.
The classic combination of two factors used in practice, the password (knowing) and the token (having), is referred to as two-factor authentication, or two-factor authentication. In everyday life, you know this example in combining a bank card (have) and PIN (know). But, of course, you can also choose to use more than two factors and increase security by adding a third factor. This method is also known as 3FA.
As you have probably noticed, the combinatorics of the different factors are not equal. In addition, there are more practical and less valuable combinations when using two or more factors. So how do you properly combine individual authentication factors?
The following table shows you the ratio of security to the chosen combination:
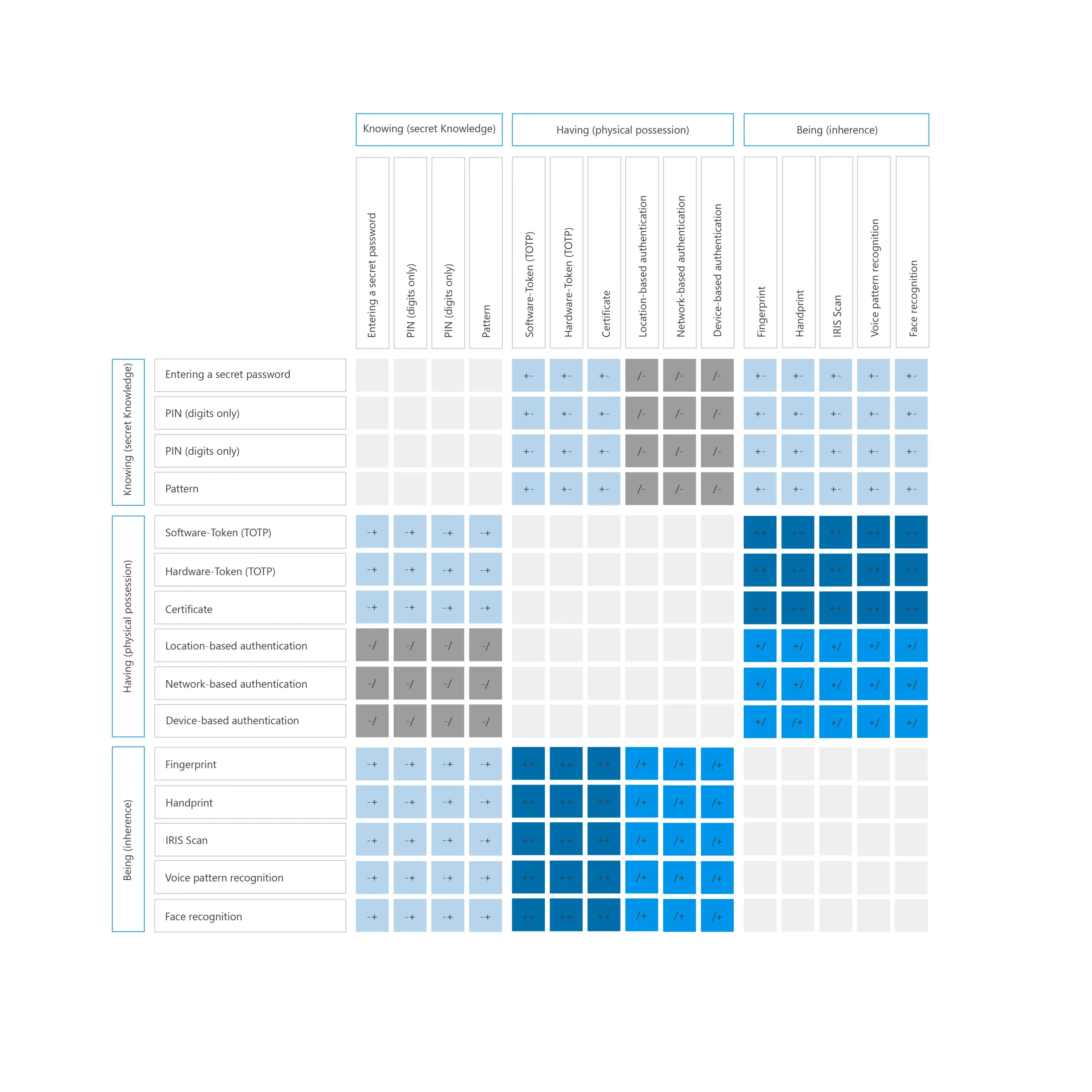
Figure 2 – Matrix Combined Use of Authentication Mechanisms
Where Do I Start?
We would also be happy to support your company with our Cybersecurity Awareness training. We highlight risks and use simple tips to teach your employees what they can and must do themselves to protect your company in the digital world.
For different application scenarios, we support you with technical and organizational measures. Depending on your company structure, we establish everything from password policies to hardware token mechanisms for protection. We also offer code reviews of your software products, quick checks of your organization, awareness training for your employees, and penetration testing of your servers and IT landscape – the entire range of security instruments in a framework from a single source, and we support you in implementing your holistic cybersecurity plan.
Together we master the future!